
Huawei Mobile WiFi E5151 and E5186 routers use insufficiently random values for DNS queries
5 Medium
CVSS2
Attack Vector
NETWORK
Attack Complexity
LOW
Authentication
NONE
Confidentiality Impact
NONE
Integrity Impact
PARTIAL
Availability Impact
NONE
AV:N/AC:L/Au:N/C:N/I:P/A:N
7.5 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
NONE
Integrity Impact
HIGH
Availability Impact
NONE
CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:H/A:N
0.003 Low
EPSS
Percentile
70.8%
Overview
Huawei Mobile WiFi E5151, firmware version 21.141.13.00.1080, and E5186, firmware version V200R001B306D01C00, use insufficiently random values for DNS queries and are vulnerable to DNS spoofing attacks.
Description
CWE-330: Use of Insufficiently Random Values- CVE-2015-8265
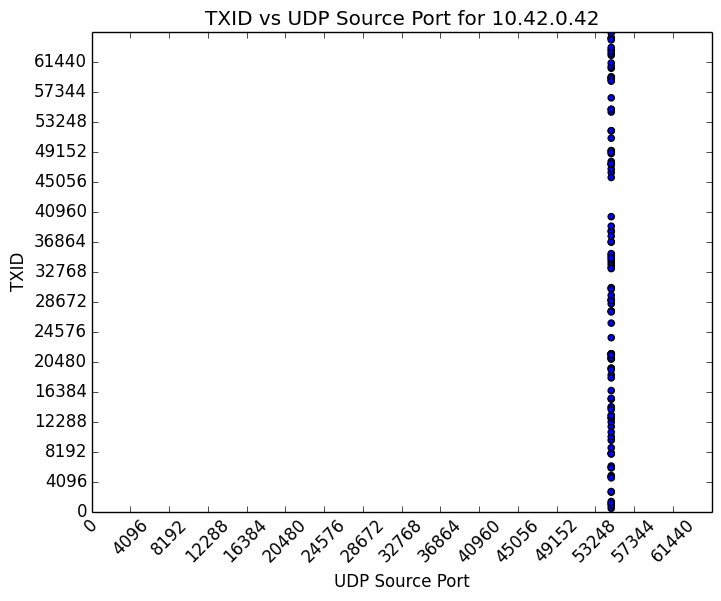
Huawei Mobile WiFi E5151 and E5186 routers use static source ports for all DNS queries originating from the local area network (LAN). An attacker with the ability to spoof DNS responses can cause E5151 or E5186 LAN clients to contact incorrect or malicious hosts under the attacker’s control.
The following graph shows a distribution of 114 DNS queries captured on the WAN port of the E5151:
Impact
A remote, unauthenticated attacker may be able to spoof DNS responses to cause E5151 or E5186 LAN clients to contact attacker-controlled hosts.
Solution
Apply an update
An update is available for the E5151 and can be obtained by contacting SmarTone at [email protected].
Huawei has released firmware version V200R001B310D01SP00C00 to address this vulnerability in the E5186. According to the vendor’s security advisory, users should contact Huawei TAC to request an upgrade.
Vendor Information
972224
Filter by status: All Affected Not Affected Unknown
Filter by content: __ Additional information available
__ Sort by: Status Alphabetical
Expand all
Javascript is disabled. Click here to view vendors.
Huawei Technologies Affected
Notified: October 08, 2015 Updated: December 10, 2015
Status
Affected
Vendor Statement
We have not received a statement from the vendor.
Vendor Information
We are not aware of further vendor information regarding this vulnerability.
CVSS Metrics
| Group | Score | Vector |
|---|---|---|
| Base | 5 | AV:N/AC:L/Au:N/C:N/I:P/A:N |
| Temporal | 3.9 | E:POC/RL:OF/RC:C |
| Environmental | 1.0 | CDP:ND/TD:L/CR:ND/IR:ND/AR:ND |
References
- <http://consumer.huawei.com/lk/mobile-broadband/mobile-wifi/tech-specs/e5151-lk.htm>
- <http://www.huawei.com/en/psirt/security-advisories/huawei-sa-20160129-01-dns-en>
Acknowledgements
These vulnerabilities were reported by Joel Land of the CERT/CC.
This document was written by Joel Land.
Other Information
| CVE IDs: | CVE-2015-8265 |
|---|---|
| Date Public: | 2016-02-01 Date First Published: |
5 Medium
CVSS2
Attack Vector
NETWORK
Attack Complexity
LOW
Authentication
NONE
Confidentiality Impact
NONE
Integrity Impact
PARTIAL
Availability Impact
NONE
AV:N/AC:L/Au:N/C:N/I:P/A:N
7.5 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
NONE
Integrity Impact
HIGH
Availability Impact
NONE
CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:H/A:N
0.003 Low
EPSS
Percentile
70.8%