
Zero-day vulnerabilities in Microsoft Exchange Server
0.975 High
EPSS
Percentile
100.0%
What happened?
On March 2, 2021 several companies released reports about in-the-wild exploitation of zero-day vulnerabilities inside Microsoft Exchange Server. The following vulnerabilities allow an attacker to compromise a vulnerable Microsoft Exchange Server. As a result, an attacker will gain access to all registered email accounts, or be able to execute arbitrary code (remote code execution or RCE) within the Exchange Server context. In the latter case, the attacker will also be able to achieve persistence on the infected server.
A total of four vulnerabilities were uncovered:
- CVE-2021-26855. Server-side request forgery (SSRF) allows an attacker without authorization to query the server with a specially constructed request that will cause remote code execution. The exploited server will then forward the query to another destination.
- CVE-2021-26857 caused by unsafe data deserialization inside the Unified Messaging service. Potentially allows an attacker to execute arbitrary code (RCE). As a result of insufficient control over user files, an attacker is able to forge a body of data query, and trick the high-privilege service into executing the code.
- CVE-2021-26858. This vulnerability allows an authorized Exchange user to overwrite any existing file inside the system with their own data. To do so, the attacker has to compromise administrative credentials or exploit another vulnerability such as SSRF CVE-2021-26855.
- CVE-2021-27065 is similar to CVE-2021-26858 and allows an authorized attacker to overwrite any system file on the Exchange server.
Kaspersky Threat Intelligence shows that these vulnerabilities are already used by cybercriminals around the world.
Geography of attacks with mentioned MS Exchange vulnerabilities (based on KSN statistics) (download)
We predict with a high degree of confidence that this is just the beginning, and we anticipate numerous exploitation attempts with the purpose of gaining access to resources inside corporate perimeters. Furthermore, we should note that there is typically a high risk of ransomware infection and/or data theft connected to such attacks.
How to protect against this threat?
Our products protect against this threat with Behavior Detection and Exploit Prevention components and detect exploitation with the following verdict: PDM:Exploit.Win32.Generic
We detect the relevant exploits with the following detection names:
- Exploit.Win32.CVE-2021-26857.gen
- HEUR:Exploit.Win32.CVE-2021-26857.a
We also detect and block the payloads (backdoors) being used in the exploitation of these vulnerabilities, according to our Threat Intelligence. Possible detection names are (but not limited to):
- HEUR:Trojan.ASP.Webshell.gen
- HEUR:Backdoor.ASP.WebShell.gen
- UDS:DangerousObject.Multi.Generic
We are actively monitoring the situation and additional detection logic will be released with updatable databases when required.
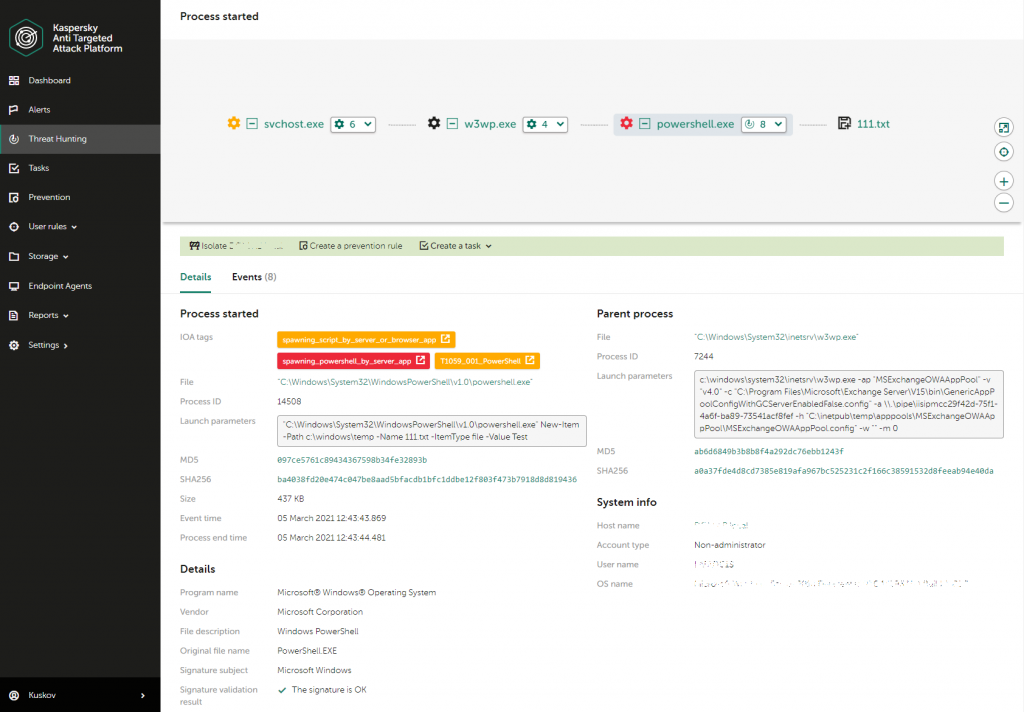
Our Endpoint Detection and Response helps to identify attacks in early stages by marking such suspicious actions with special IoA tags (and creating corresponding alerts). For example, this is an example of Powershell started by IIS Worker process (w3wp.exe) as a result of vulnerability exploitation:
Our Managed Detection and Response service is also able to identify and stop this attack by using threat hunting rules to spot the exploitation itself, as well as possible payload activity.
And the thorough research of the attack will soon be available within APT Intelligence Reporting service, please contact [email protected] for details.
Recommendations
- As Microsoft has already released an update to fix all these vulnerabilities, we strongly recommend updating Exchange Server as soon as possible.
- Focus your defense strategy on detecting lateral movements and data exfiltration to the internet. Pay special attention to outgoing traffic to detect cybercriminal connections. Back up data regularly. Make sure you can quickly access it in an emergency.
- Use solutions like Kaspersky Endpoint Detection and Response and the Kaspersky Managed Detection and Response service which help to identify and stop the attack in the early stages, before the attackers achieve their goals.
- Use a reliable endpoint security solution such as Kaspersky Endpoint Security for Business that is powered by exploit prevention, behavior detection and a remediation engine that is able to roll back malicious actions. KESB also has self-defense mechanisms that can prevent its removal by cybercriminals.