Major Instagram App Bug Could've Given Hackers Remote Access to Your Phone
EPSS
Percentile
36.4%
Ever wonder how hackers can hack your smartphone remotely?
In a report shared with The Hacker News today, Check Point researchers disclosed details about a critical vulnerability in Instagram’s Android app that could have allowed remote attackers to take control over a targeted device just by sending victims a specially crafted image.
What’s more worrisome is that the flaw not only lets attackers perform actions on behalf of the user within the Instagram app—including spying on victim’s private messages and even deleting or posting photos from their accounts—but also execute arbitrary code on the device.
According to an advisory published by Facebook, the heap overflow security issue (tracked as CVE-2020-1895, CVSS score: 7.8) impacts all versions of the Instagram app prior to 128.0.0.26.128, which was released on February 10 earlier this year.
“This [flaw] turns the device into a tool for spying on targeted users without their knowledge, as well as enabling malicious manipulation of their Instagram profile,” Check Point Research said in an analysis published today.
“In either case, the attack could lead to a massive invasion of users’ privacy and could affect reputations — or lead to security risks that are even more serious.”
After the findings were reported to Facebook, the social media company addressed the issue with a patch update released six months ago. The public disclosure was delayed all this time to allow the majority of Instagram’s users to update the app, thereby mitigating the risk this vulnerability may introduce.
Although Facebook confirmed there were no signs that this bug was exploited globally, the development is another reminder of why it’s essential to keep apps up to date and be mindful of the permissions granted to them.
A Heap Overflow Vulnerability
According to Check Point, the memory corruption vulnerability allows for remote code execution that, given Instagram’s extensive permissions to access a user’s camera, contacts, GPS, photo library, and microphone, could be leveraged to perform any malicious action on the infected device.
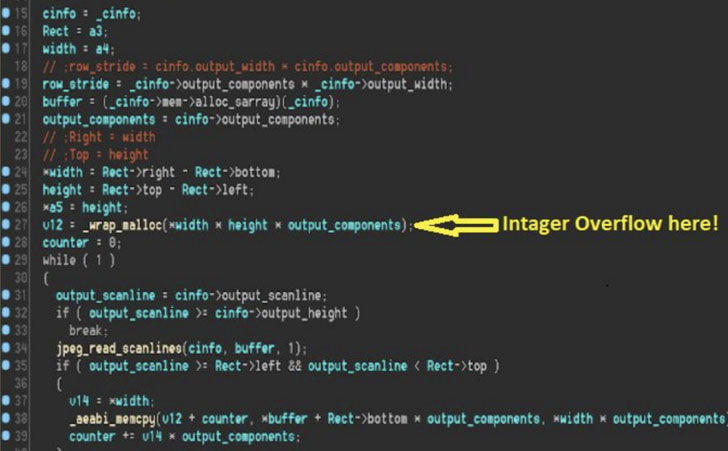
As for the flaw itself, it stems from the way Instagram integrated MozJPEG — an open-source JPEG encoder library which aims to lower bandwidth and provide better compression for images uploaded to the service — resulting in an integer overflow when the vulnerable function in question (“read_jpg_copy_loop”) attempts to parse a malicious image with specially crafted dimensions.
In doing so, an adversary could gain control over the size of the memory allocated to the image, the length of the data to be overwritten, and lastly, the contents of the overflowed memory region, in turn giving the attacker the ability to corrupt specific locations in a heap and divert code execution.
The consequence of such a vulnerability is that all a bad actor needs to do is send a corrupted JPEG image to a victim via email or WhatsApp. Once the recipient saves the image to the device and launches Instagram, the exploitation takes place automatically, granting the attacker full control over the app.
Even worse, the exploit can be used to crash a user’s Instagram app and render it inaccessible unless it’s removed and reinstalled all over again on the device.
If anything, the vulnerability is indicative of how incorporating third-party libraries into apps and services can be a weak link for security if the integration is not done right.
“Fuzzing the exposed code turned up some new vulnerabilities which have since been fixed,” Check Point’s Gal Elbaz said. "It is likely that, given enough effort, one of these vulnerabilities can be exploited for RCE in a zero-click attack scenario.
“Unfortunately, it is also likely that other bugs remain or will be introduced in the future. As such, continuous fuzz-testing of this and similar media format parsing code, both in operating system libraries and third-party libraries, is absolutely necessary.”
Yaniv Balmas, the head of cyber research at Check Point, provided the following safety tips for smartphone users:
- **Update! Update! Update!**Make sure you regularly update your mobile application and your mobile operating systems. Dozens of critical security patches are being shipped out in these updates every week, and each one can potentially have a severe impact on your privacy.
- Monitor permissions. Pay better attention to applications asking for permission. It’s effortless for app developers to ask the users for excessive permissions, and it’s also very easy for users to click ‘Allow’ without thinking twice.
- Think twice about approvals. Take a few seconds to think before you approve anything. Ask: “do I really want to give this application this kind of access, do I really need it?” if the answer is no, DO NOT APPROVE.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.